Debt collection agencies handle large volumes of sensitive financial and personal data, yet many still rely on fragmented systems that increase exposure to breaches and compliance gaps. The global average cost of a data breach has reached $4.4 million, according to IBM.
That is not just a security issue. It is an operational and financial risk that directly impacts recovery, trust, and regulatory standing. As expectations around data protection rise, agencies need systems built for both control and scale.
This is where SOC-2-compliant debt-collection white-label solutions come into focus. In this guide, we break down what SOC 2 means, why it matters, and what to look for in a secure platform.
SOC 2 compliance is an independently audited framework developed by the American Institute of Certified Public Accountants (AICPA) to evaluate how organizations manage and protect customer data. It is based on five criteria: security, availability, processing integrity, confidentiality, and privacy.
For debt collection agencies, this goes beyond IT systems. It covers how consumer data is accessed, processed, stored, and communicated across the entire workflow. Unlike regulatory laws, SOC 2 is not mandatory. However, it acts as a structured standard that demonstrates whether your systems and processes can securely handle sensitive financial information at scale.
Importance of SOC-2 compliance in debt collection:
In the next section, we examine where standard white-label debt collection platforms fall short in meeting these expectations.
Suggested Read: Understanding Compliance in Debt Collection: Information and Protection
Most white-label platforms prioritize branding over backend control, leaving agencies dependent on vendor-defined systems. This limits visibility into how consumer data moves across payments, communication, and integrations, creating hidden compliance and security risks.
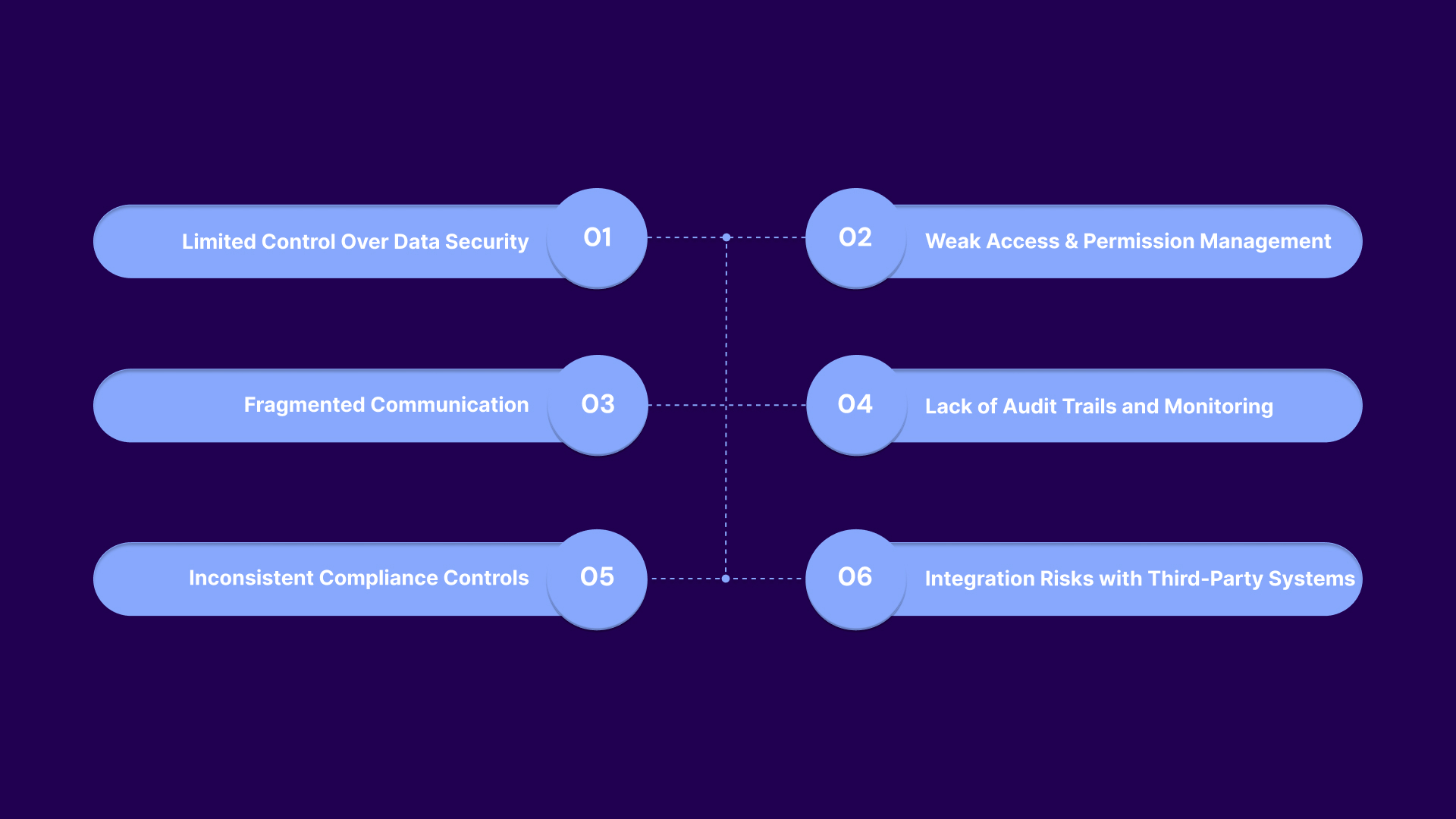
These are the common gaps in traditional collection platforms:
Agencies often cannot configure encryption standards, data retention policies, or storage locations at a granular level. This means sensitive consumer data may be stored or transmitted without alignment to internal security policies or client requirements.
Many platforms offer only broad user roles, without field-level or action-based restrictions. Agents may have unnecessary access to full account details, increasing the risk of data exposure or misuse.
Calls, SMS, email, and payment processing are frequently handled through separate modules or third-party tools. This creates gaps in data tracking, making it difficult to enforce consistent compliance across all touchpoints.
Systems may not log detailed user actions such as payment edits, account access, or communication changes. Without this, agencies cannot reconstruct events during disputes or demonstrate compliance during audits.
Communication timing, consent tracking, and disclosure requirements are often managed manually or outside the platform. This increases the likelihood of violations under laws like the Fair Debt Collection Practices Act (FDCPA).
APIs and external tools may transmit data without proper validation, tokenization, or encryption controls. This exposes sensitive information during handoffs between systems.
Tratta addresses these gaps by embedding security, access control, and auditability directly into core workflows. It meets top security standards, including PCI DSS Level 1 and SOC 2 Type II. Payment data is encrypted, continuously monitored, and securely processed across all workflows. Schedule a free demo today.
Choosing the right platform goes beyond checking for a SOC 2 report. Agencies need to assess how deeply security, access control, and compliance are embedded into everyday workflows, not just documented at a policy level.
Core features to look for:
SOC 2 compliant systems must enforce encryption standards across all data states, including storage, transmission, and processing. This ensures that sensitive consumer and payment data is protected at every interaction point.
Key controls to evaluate include:
Strong access control ensures that only authorized users can view or act on specific data. SOC 2 emphasizes least-privilege access to minimize internal risk and unauthorized actions.
Look for the following capabilities:
SOC 2 requires systems to maintain detailed logs of user activity and system events. This creates traceability and supports faster detection of anomalies or unauthorized actions.
Important features include:
Compliance should be embedded into how the system operates, not managed externally. This ensures that every interaction aligns with regulatory requirements automatically.
Evaluate whether the platform includes:
Handling payments is one of the highest-risk areas in collections. SOC 2-compliant platforms must ensure that payment data is processed securely and not exposed unnecessarily.
Check for:
Integrations are often the weakest point in a system if not properly secured. SOC 2 evaluates how data moves between systems and whether those exchanges are controlled and monitored.
Look for:
In the next section, we connect these features to real outcomes by examining how SOC 2 compliance improves debt recovery for collection agencies.
Suggested Read: Innovative Approaches to Future Debt Collection Strategies
SOC 2 compliance is often viewed as a security framework, but its real impact is operational. By enforcing structured controls across data, access, and workflows, it directly improves the consistency and efficiency with which agencies recover payments.
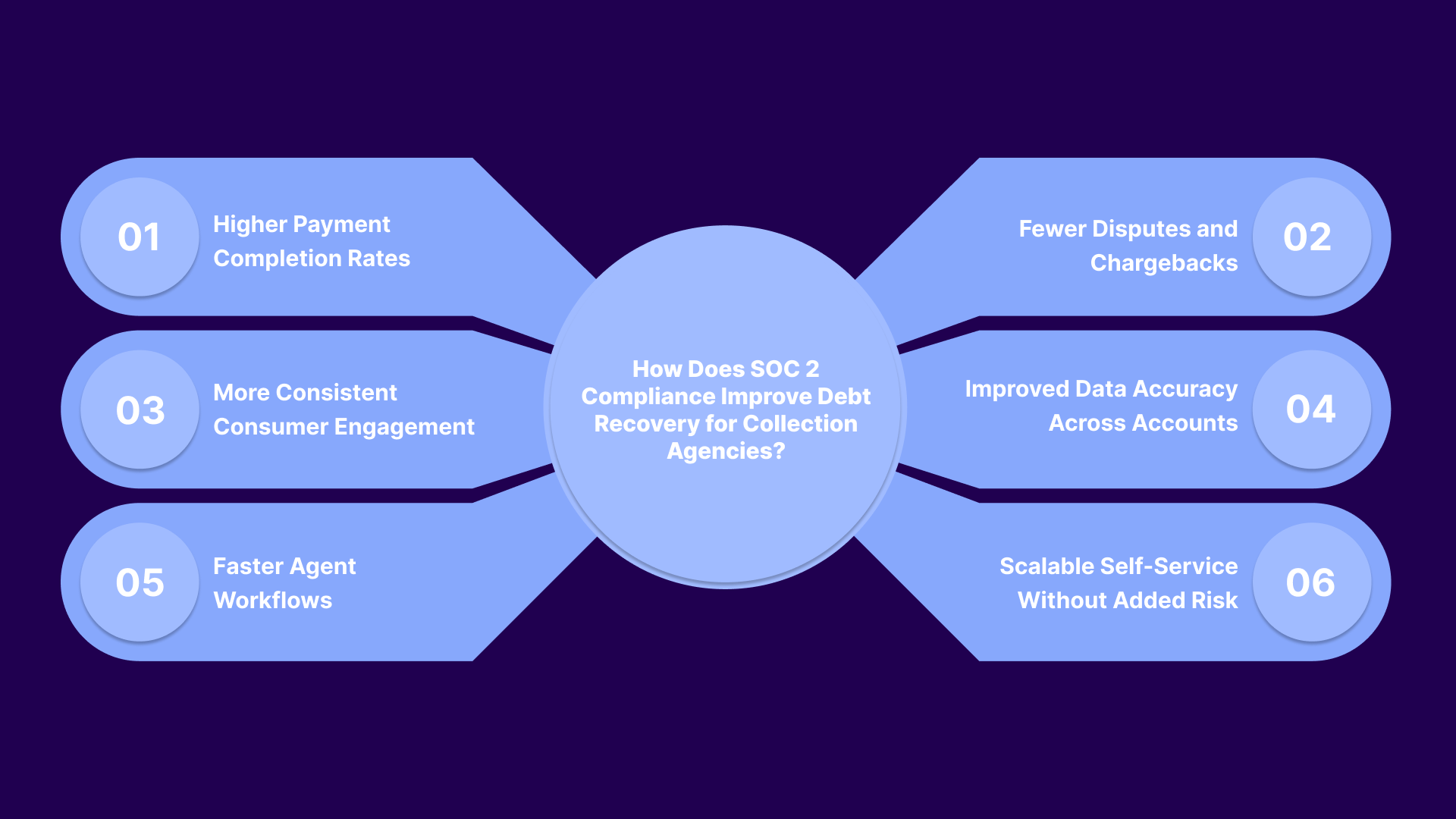
Benefits include:
These points show how secure environments influence consumer willingness to complete payments.
These points focus on how traceability reduces revenue leakage and resolution time.
These points highlight how compliance controls stabilize outreach performance.
These points explain how controlled systems reduce errors in account handling.
These points show how structured systems reduce operational friction for agents.
These points demonstrate how secure automation supports growth without increasing exposure.
Tratta operationalizes SOC 2 controls by embedding them directly into day-to-day collection workflows. Access, payments, and consumer interactions are governed by consistent rules, logging, and validation at every step. Get in touch with us to learn more.
Data breaches in debt collection expose highly sensitive financial and personal information, often across multiple systems and vendors. The impact creates legal exposure, operational disruption, and direct revenue loss.
This is what happens after a breach:
Agencies may face investigations by regulators such as the Consumer Financial Protection Bureau (CFPB) and state authorities. Violations tied to unfair practices or data misuse can trigger penalties under laws such as the Fair Debt Collection Practices Act (FDCPA).
Consumers affected by data exposure can file lawsuits for damages related to privacy violations or financial harm. Class actions can significantly increase legal costs and settlement payouts.
U.S. state data breach laws require agencies to notify affected individuals, often within strict timelines. This includes disclosure of what data was exposed and may involve regulatory reporting obligations.
Exposed payment credentials or personal data can be used for unauthorized transactions or identity theft. This leads to chargebacks, reversals, and financial liability for the agency.
Systems may need to be taken offline to investigate and contain the breach. This halts collection activities, delays payments, and creates a backlog across accounts.
In the next section, we shift from risk to prevention by examining what a secure, compliance-driven collection infrastructure looks like in practice. Choosing the right technology is not just about features. It is about embedding control, visibility, and protection into every part of the collection process.
.jpg)
Tratta is an end-to-end debt collection platform built to help agencies increase recovery while maintaining strict control over data, payments, and communication. It combines consumer engagement, payment processing, and workflow automation into a single system designed specifically for collection operations.
From a security & compliance perspective, Tratta is structured to minimize breach risk through encryption, secure gateway integrations, role-based access controls, and continuous system monitoring. Sensitive data is not stored directly within the platform environment. All communications are protected using industry-standard security protocols, reducing exposure across the collection lifecycle.
Beyond security, the platform connects these controls to operational outcomes by embedding them into the features agencies use every day. Other key features include:
Tratta also reduces the time and complexity typically associated with onboarding new systems. Our onboarding process is designed to help agencies go live quickly with minimal disruption, allowing teams to start improving recovery performance without long implementation cycles.
Without the right controls in place, debt collection operations become vulnerable to more than just data breaches. Inconsistent workflows, poor visibility, and weak access controls can lead to compliance violations, lost revenue, and damaged client relationships, all of which are difficult to recover from.
Tratta addresses this by bringing structure and accountability into every layer of the collection process. Its platform aligns security, communication, and payment workflows so agencies can operate with clarity, consistency, and confidence at scale.
See how a compliance-driven system can strengthen your recovery strategy. Request a demo and explore how to move from reactive controls to built-in protection.
No, SOC 2 is not mandated by law for debt collectors. However, it is often required by clients and acts as a recognized standard for demonstrating strong data security controls.
Yes, SOC 2 evaluates how third-party integrations handle data, including APIs and external systems. Agencies must ensure vendors follow secure data handling practices to avoid introducing vulnerabilities.
Yes, smaller agencies benefit by standardizing security practices early. This improves client trust, reduces operational risk, and positions them competitively when working with larger creditors or regulated industries.
SOC 2 focuses on overall data security and operational controls, while PCI DSS specifically governs payment card data handling. Both are complementary and important for agencies processing consumer payments securely.
Many creditors require vendors to demonstrate strong data controls before sharing accounts. SOC 2 compliance helps agencies meet these expectations and reduces friction during onboarding and contract approvals.