
Collection agencies are expected to demonstrate airtight control over how consumer data is accessed, processed, and secured. This extends beyond internal operations to creditors, auditors, and partners. Yet many still operate across fragmented systems where access controls, logging, and oversight are difficult to standardize or prove.
This creates real exposure, especially when the average cost of a data breach has reached $4.44 million globally. If you are facing client due diligence, audits, or vendor reviews, you already know the pressure is not theoretical.
In this article, we break down what SOC 2 Type II certification means for collection agencies and why it is becoming a baseline requirement in 2026.
A SOC 2 Type II certification assesses how effectively an organization’s controls perform over time in real operating conditions. In debt collection, this directly applies to how consumer data is accessed, processed, and secured across systems and workflows. Rather than focusing on intent, it validates execution under live conditions.
Key components involved in SOC 2 Type II certification include:
SOC 2 Type II is ultimately about proving that controls work in practice, not just on paper. In the next section, we will break down how it differs from Type I and why that distinction matters for collection agencies.
Suggested Read: Importance of Compliance Management System in Debt Collection
SOC 2 reports are issued by independent auditors under the American Institute of Certified Public Accountants (AICPA) framework. While both Type I and Type II evaluate an organization’s controls against the Trust Services Criteria, they differ in how deeply those controls are tested.
Table showing differences in SOC Type 1 and Type 2 certifications:
The choice between Type I and Type II depends on an agency's compliance maturity and the expectations of stakeholders during due diligence.
Key implications:
Tratta embeds controls such as access management, activity logging, and payment-level tracking directly into workflows, making it easier to demonstrate consistent control performance over time. This reduces the operational burden of maintaining audit readiness while supporting continuous compliance. Schedule a free demo.
Risk in debt collection focuses on specific workflows in which sensitive data is accessed, processed, or transferred without consistent controls. SOC 2 Type II directly addresses these areas by enforcing structured oversight, continuous monitoring, and verifiable control execution.
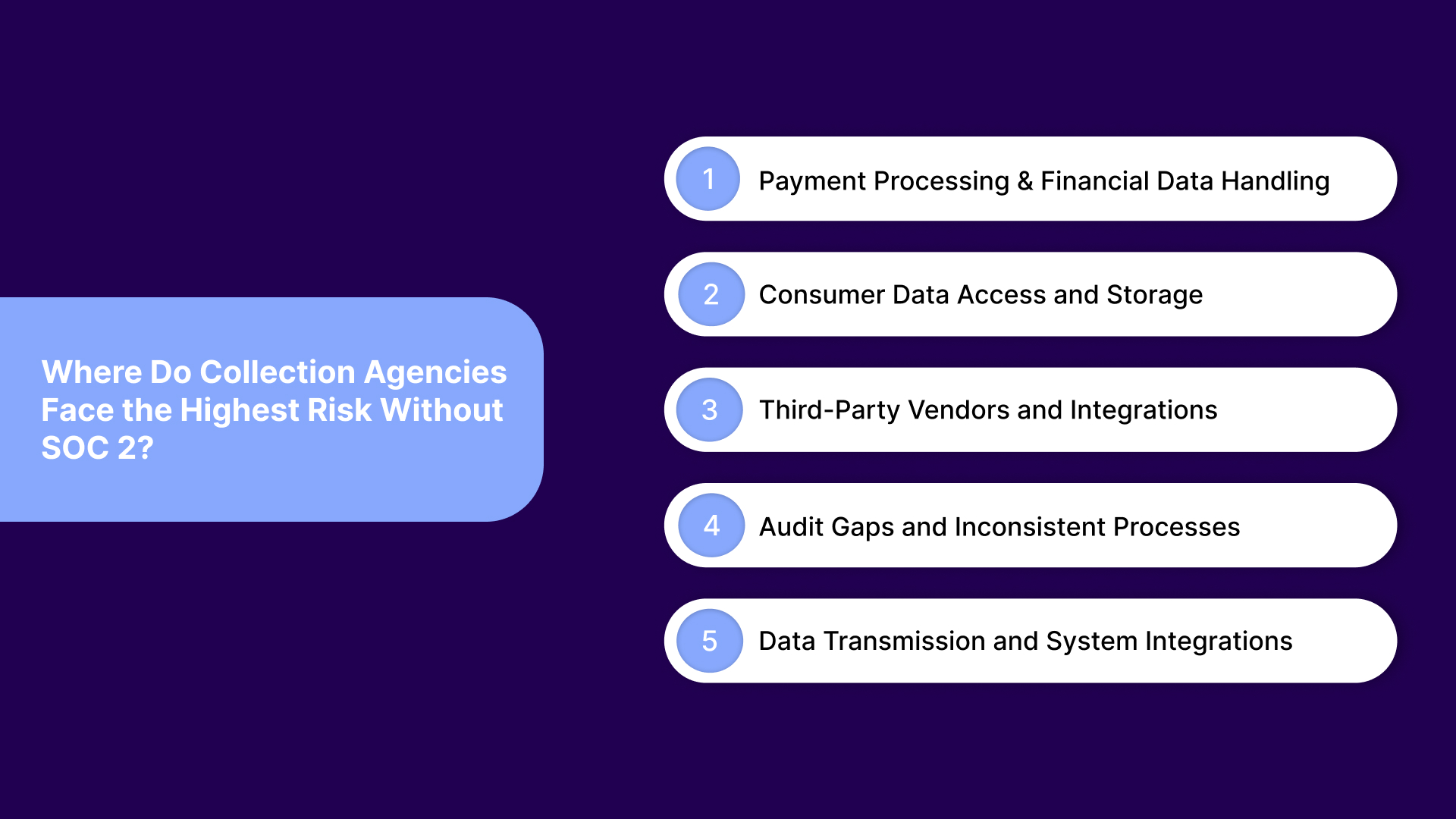
These are a few areas where SOC 2 certifications help:
Payment workflows involve high-risk transactions where errors, unauthorized actions, or inconsistent validation can lead to financial and compliance exposure. Without SOC 2, these processes often rely on fragmented systems and manual checks, increasing the likelihood of failure. SOC 2 introduces control validation and auditability into every transaction layer.
This is where it strengthens control and reduces exposure:
Collection agencies manage large volumes of personal and financial data across multiple systems. Without structured access controls and monitoring, unauthorized access and data misuse become significant risks. SOC 2 ensures that access is controlled, monitored, and continuously reviewed.
How SOC 2 brings consistency and oversight to this area:
Agencies depend on multiple vendors for payments, communication, and data processing. Each integration introduces risk if controls are not aligned or validated across systems. SOC 2 extends oversight into third-party relationships through standardized control expectations.
This is where SOC 2 improves control visibility and reduces gaps:
Inconsistent workflows and a lack of documentation create significant audit challenges. Without SOC 2, agencies often struggle to prove how controls are applied in practice. SOC 2 ensures processes are standardized, documented, and continuously tested.
This is how SOC 2 reduces uncertainty and strengthens oversight:
Data does not stay within one system in collections. It moves across payment processors, CRMs, dialers, and communication tools, increasing exposure at every transfer point. Without SOC 2, these integrations often lack consistent validation, encryption standards, and monitoring.
How SOC 2 enforces control across this workflow:
SOC 2 Type II does not eliminate risk, but it structures how risk is managed and validated across operations. In the next section, we will examine why this level of control is becoming a competitive requirement for collection agencies.
Suggested Read: Innovative Approaches to Future Debt Collection Strategies
SOC 2 Type II is not legally mandatory for collection agencies. However, it is increasingly required during client onboarding, vendor due diligence, and RFP evaluations, especially when handling financial and personal data.
This shift is being driven by clear market expectations:
Tratta embeds regulatory requirements into workflows through a compliance-by-code architecture. The platform includes built-in controls such as role-based access, encrypted payment processing, audit-ready records, and continuous monitoring, helping agencies demonstrate consistent control performance. Contact us to learn more.
Collection agencies operate within multiple compliance frameworks, each addressing a different layer of risk. SOC 2 Type II focuses on how systems and controls perform over time, while other standards govern payments, data security, or collection practices.
Table showing how different standards apply to debt collection:
SOC 2 Type II does not replace these standards. It works alongside them by ensuring that the controls supporting these requirements are consistently applied, monitored, and validated over time. In the next section, we will examine what collection agencies should consider when choosing a SOC 2 Type II–aligned platform.
Suggested Read: Machine Learning Tools for Customer Risk Assessment in Collections
SOC 2 Type II is not achieved solely through policy. It depends on systems that can enforce, monitor, and prove control effectiveness across daily operations.
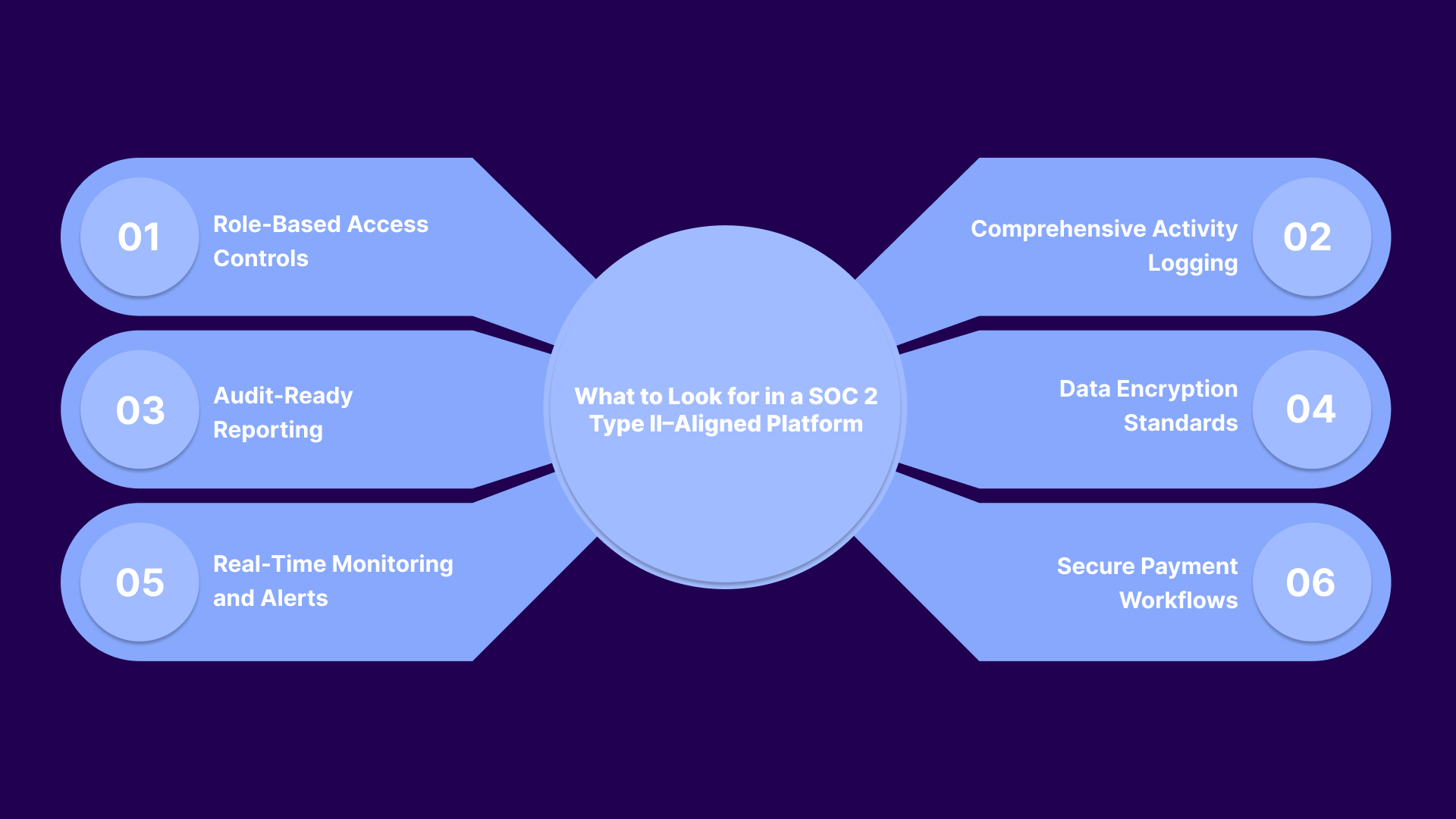
When evaluating a SOC 2 Type II–aligned platform, focus on features that support continuous control execution:
Platforms built specifically for collections make this easier to achieve. In the next section, we will look at how a purpose-built platform brings these features together to support both compliance and recovery performance.
Suggested Read: Understanding the Importance and Process of Digital Debt Collection
Tratta is a digital debt collection and payment platform built for agencies operating in highly regulated environments. It combines payments, communication, automation, and compliance into a single system. The platform is designed to reduce fragmentation and bring consistency to workflows that are typically difficult to audit and standardize.
Tratta structures system-level compliance by standardizing how data, payments, and interactions are handled across workflows. The platform supports standards such as SOC 2 Type II and PCI DSS, with features including encrypted payment processing, tokenization (so raw card data is never stored), role-based access controls, multi-factor authentication, and continuous monitoring.
Tratta offers a broader feature set that supports both recovery and operational control:
Tratta is not just a compliance layer. It is a system that embeds control into execution, making it easier to maintain SOC 2 standards without adding operational complexity. With fast onboarding, flexible integrations, and dedicated support, agencies can transition quickly and start improving both compliance and recovery performance with minimal disruption.
Without SOC 2 Type II–level controls, collection agencies face growing pressure from audits, client due diligence, and data security expectations. Gaps in access control, monitoring, or documentation slow down operations and limit growth opportunities. Over time, this makes it harder to win contracts, maintain trust, and scale efficiently.
Tratta addresses this by embedding compliance, security, and payment workflows into a single system designed for regulated collections. Its infrastructure supports continuous control execution, audit-ready reporting, and secure data handling, helping agencies meet SOC 2 expectations while improving operational performance.
Strengthen your compliance posture without adding complexity to your workflows. Schedule a free call today.
SOC 2 Type II certification verifies that a collection agency’s security and operational controls function effectively over time, ensuring consistent protection of consumer data across workflows, systems, and payment processes.
SOC 2 Type II certification usually takes 3 to 12 months, including readiness preparation, control implementation, and the audit observation period, where controls are tested over time for effectiveness.
Collection agencies achieve SOC 2 certification by implementing the required controls, aligning their systems with the Trust Services Criteria, documenting their processes, and undergoing an independent audit conducted by a licensed CPA firm.
SOC 2 Type II certification is not legally required, but many creditors and partners expect it during vendor selection, making it increasingly important for winning contracts and maintaining trust.
SOC 2 Type II includes controls around data security and processing integrity, but it does not replace PCI DSS. Agencies handling card payments must comply with both standards.